Welcome back, my greenhorn hackers.
When Wi-Fi was first developed in the late 1990s, Wired Equivalent Privacy was created to give wireless communications confidentiality. WEP, as it became known, proved terribly flawed and easily cracked. You can read more about that in my beginner's guide to hacking Wi-Fi.
As a replacement, most wireless access points now use Wi-Fi Protected Access II with a pre-shared key for wireless security, known as WPA2-PSK. WPA2 uses a stronger encryption algorithm, AES, that's very difficult to crack—but not impossible. My beginner's Wi-Fi hacking guide also gives more information on this.
This article teaches you how to easily crack WPA/WPA2 Wi-Fi passwords using the Aircrack-Ng suite In Kali Linux. Not only will you learn the basics, but I will also provide you the best tips and educational resources on increasing your chances of executing successful dictionary-based brute force attacks on captured WPA handshakes. Let’s start the wifi hacking with Kali linux. With kali linux’s Air Crack tool you can know wifi password. Kali Linux is available with a full suite of applications to crack or hack Wifi networks, including Aircrack and Reaver – which we both mentioned before to crack WEP and WPA passwords respectively.
export JAVAHOME=jdk-install-dir. add:$JAVAHOME/bin to the PATH variableOn linux:. Enter the variable name as JAVAHOME. Enter the variable value as the installation path for the JavaDevelopment Kit. Free jdk download for mac.
Instantly preview your video, and then create clips to post on your social networks.The app also lets you remotely control camera and camcorder functions like cycle recording, time stamping, video and camera resolution, frame rate, time delay, slow-motion video, and more.The cutest, most fun action lifestyle camera now lets you connect, control, and share easier than ever with built-in Wi-Fi. Polaroid cube mac app download.
The weakness in the WPA2-PSK system is that the encrypted password is shared in what is known as the 4-way handshake. When a client authenticates to the access point (AP), the client and the AP go through a 4-step process to authenticate the user to the AP. If we can grab the password at that time, we can then attempt to crack it.
Crack WPA/WPA2 Wi-Fi Routers with Airodump-ng and Aircrack-ng/Hashcat.
This is a brief walk-through tutorial that illustrates how to crack Wi-Fi networks that are secured using weak passwords. It is not exhaustive, but it should be enough information for you to test your own network's security or break into one nearby. The attack outlined below is entirely passive (listening only, nothing is broadcast from your computer) and it is impossible to detect provided that you don't actually use the password that you crack. An optional active deauthentication attack can be used to speed up the reconnaissance process and is described at the end of this document.
If you are familiar with this process, you can skip the descriptions and jump to a list of the commands used at the bottom. For a variety of suggestions and alternative methods, see the appendix. neal1991 and tiiime have also graciously provided translations to this document and the appendix in Chinese if you prefer those versions.
DISCLAIMER: This software/tutorial is for educational purposes only. It should not be used for illegal activity. The author is not responsible for its use. Don't be a dick.
Getting Started
This tutorial assumes that you:
- Have a general comfortability using the command-line
- Are running a debian-based linux distro, preferably Kali linux (OSX users see the appendix)
- Have Aircrack-ng installed
sudo apt-get install aircrack-ng
- Have a wireless card that supports monitor mode (see here for a list of supported devices)
Cracking a Wi-Fi Network
Monitor Mode
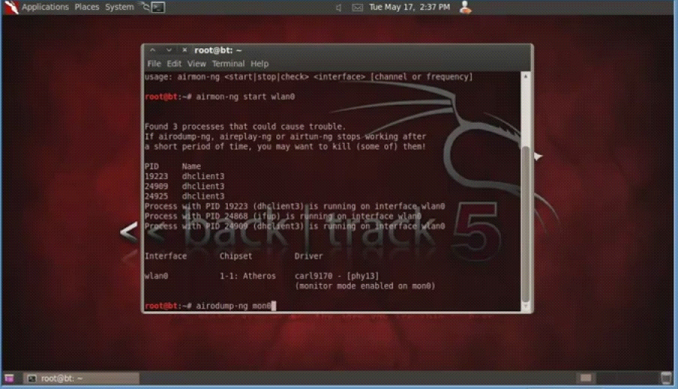
Begin by listing wireless interfaces that support monitor mode with:
If you do not see an interface listed then your wireless card does not support monitor mode
We will assume your wireless interface name is wlan0 but be sure to use the correct name if it differs from this. Next, we will place the interface into monitor mode:
Download the latest Lexmark 2600 Series driver for your computer's operating system. All downloads available on this website have been scanned by the latest anti-virus software and are guaranteed to be virus and malware-free. Lexmark 2600 series free download - Lexmark 1200 Series, Lexmark 2400 Series, Lexmark 2500 Series, and many more programs. Lexmark 2600 printer download free download - Apple Lexmark Printer Drivers, Lexmark Tools For Office, Gimp-Print, and many more programs. Free lexmark 2600 printer download. Lexmark 2600 Series Reviews – Is a multifunctional All-In-One printer that provides fast print speed and convenience in use. With a very affordable price also environmentally friendly, Lexmark Printer 2600 can do photo printing size 4 × 6 inches and 5 × 7 inches takes 44 sec with good quality and beautiful, also very suitable for the original colour because this printer uses a print. Lexmark X2600 printer series Full Driver & Software Package download for Microsoft Windows and MacOS X Operating Systems. Lexmark printer driver is an application software program that works on a computer to communicate with a printer.
Run iwconfig. You should now see a new monitor mode interface listed (likely mon0 or wlan0mon).
Find Your Target
Start listening to 802.11 Beacon frames broadcast by nearby wireless routers using your monitor interface:
You should see output similar to what is below.
For the purposes of this demo, we will choose to crack the password of my network, 'hackme'. Dji assistant 1.1 2 download mac. Remember the BSSID MAC address and channel (CH) number as displayed by airodump-ng, as we will need them both for the next step.
Capture a 4-way Handshake
WPA/WPA2 uses a 4-way handshake to authenticate devices to the network. You don't have to know anything about what that means, but you do have to capture one of these handshakes in order to crack the network password. These handshakes occur whenever a device connects to the network, for instance, when your neighbor returns home from work. We capture this handshake by directing airmon-ng to monitor traffic on the target network using the channel and bssid values discovered from the previous command.
Now we wait. Once you've captured a handshake, you should see something like [ WPA handshake: bc:d3:c9:ef:d2:67 at the top right of the screen, just right of the current time.
If you are feeling impatient, and are comfortable using an active attack, you can force devices connected to the target network to reconnect, be sending malicious deauthentication packets at them. This often results in the capture of a 4-way handshake. See the deauth attack section below for info on this.
Once you've captured a handshake, press ctrl-c to quit airodump-ng. You should see a .cap file wherever you told airodump-ng to save the capture (likely called -01.cap). We will use this capture file to crack the network password. I like to rename this file to reflect the network name we are trying to crack:
Crack the Network Password
The final step is to crack the password using the captured handshake. If you have access to a GPU, I highly recommend using hashcat for password cracking. I've created a simple tool that makes hashcat super easy to use called naive-hashcat. If you don't have access to a GPU, there are various online GPU cracking services that you can use, like GPUHASH.me or OnlineHashCrack. You can also try your hand at CPU cracking with Aircrack-ng.
Note that both attack methods below assume a relatively weak user generated password. Most WPA/WPA2 routers come with strong 12 character random passwords that many users (rightly) leave unchanged. If you are attempting to crack one of these passwords, I recommend using the Probable-Wordlists WPA-length dictionary files.
Cracking With naive-hashcat (recommended)
Before we can crack the password using naive-hashcat, we need to convert our .cap file to the equivalent hashcat file format .hccapx. You can do this easily by either uploading the .cap file to https://hashcat.net/cap2hccapx/ or using the cap2hccapx tool directly.
Next, download and run naive-hashcat:
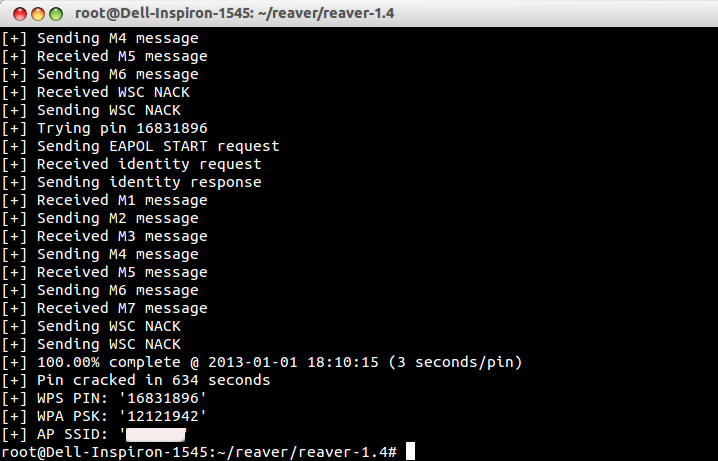
Naive-hashcat uses various dictionary, rule, combination, and mask (smart brute-force) attacks and it can take days or even months to run against mid-strength passwords. The cracked password will be saved to hackme.pot, so check this file periodically. Once you've cracked the password, you should see something like this as the contents of your POT_FILE:
Terraria inventory editor mac download. Where the last two fields separated by : are the network name and password respectively.
If you would like to use hashcat without naive-hashcat see this page for info.
Cracking With Aircrack-ng
Aircrack-ng can be used for very basic dictionary attacks running on your CPU. Before you run the attack you need a wordlist. I recommend using the infamous rockyou dictionary file:
Note, that if the network password is not in the wordfile you will not crack the password.
There are some built-in defaults that Zoom offers, but you can also select a picture stored on your phone or Mac. If you're using Zoom for your meetings or to connect with friends and family, you can always spice things up with virtual backgrounds.Virtual backgrounds are kind of like having a green screen behind you, meaning you can choose any picture you want to display behind you in a Zoom call. Since the entire world is trying to more lately, Zoom has seen a use increase in use. How to create ios app without mac. Zoom offers a unified communications platform that provides video meetings, voice, webinars, and chat across multiple platforms, including desktops, phones, mobile devices, and conference room systems.
If the password is cracked you will see a KEY FOUND! message in the terminal followed by the plain text version of the network password.
Deauth Attack
A deauth attack sends forged deauthentication packets from your machine to a client connected to the network you are trying to crack. These packets include fake 'sender' addresses that make them appear to the client as if they were sent from the access point themselves. Upon receipt of such packets, most clients disconnect from the network and immediately reconnect, providing you with a 4-way handshake if you are listening with airodump-ng.
Use airodump-ng to monitor a specific access point (using -c channel --bssid MAC) until you see a client (STATION) connected. A connected client look something like this, where is 64:BC:0C:48:97:F7 the client MAC.
Now, leave airodump-ng running and open a new terminal. We will use the aireplay-ng command to send fake deauth packets to our victim client, forcing it to reconnect to the network and hopefully grabbing a handshake in the process.
IPadian Windows XP/7/8/10 full. download free torrent. Each time you open an application in iPadian, a browser window opens. On the right side you will find another list of applications that you can click on the shortcuts. For example, when you search, you see a. https://cacconfecsi.tistory.com/14. May 29, 2018 iPadian is made to transform your Windows PC into an Apple device which can support and run applications specially designed for iOS. It is a simulator that can help you to test applications or to play iOS games directly on your computer. This program is working in full screen, but if you want to access your desktop, you have dedicated buttons the right side of the screen. IPadian 3.0 portable 64-Bit download torrent. Download here: IPadian useful tool that simulates the iPad interface on your Windows desktop. If you are serious iPad fan, this is your chance to make your Windows PC takes on the appearance of the iPad is impressive graphical interface. May 14, 2017 Download iPadian 2019 for Windows Download iPadian 2019 for Windows – If you have actually ever seen the commercials for Apple items, you may be fascinated to really attempt them out without making a huge purchase. With iPadian 2019, you can play around with attributes and also tools which look and also act like those.
You can optionally broadcast deauth packets to all connected clients with:
Once you've sent the deauth packets, head back over to your airodump-ng process, and with any luck you should now see something like this at the top right: [ WPA handshake: 9C:5C:8E:C9:AB:C0. Now that you've captured a handshake you should be ready to crack the network password.
List of Commands
Below is a list of all of the commands needed to crack a WPA/WPA2 network, in order, with minimal explanation. Ratne igre download. Download mac ip address changer.
Appendix
The response to this tutorial was so great that I've added suggestions and additional material from community members as an appendix. Check it out to learn how to:
- Capture handshakes and crack WPA passwords on MacOS/OSX
- Capture handshakes from every network around you with
wlandump-ng - Use
crunchto generate 100+GB wordlists on-the-fly - Spoof your MAC address with
macchanger

A Chinese version of the appendix is also available.
Attribution
Much of the information presented here was gleaned from Lewis Encarnacion's awesome tutorial. Thanks also to the awesome authors and maintainers who work on Aircrack-ng and Hashcat.
How To Crack Wifi Wpa2 Psk Password
Overwhelming thanks to neal1991 and tiiime for translating this tutorial into Chinese. Further shout outs to yizhiheng, hiteshnayak305, enilfodne, DrinkMoreCodeMore, hivie7510, cprogrammer1994, 0XE4, hartzell, zeeshanu, flennic, bhusang, tversteeg, gpetrousov, crowchirp and Shark0der who also provided suggestions and typo fixes on Reddit and GitHub. Download office 2011 for mac. If you are interested in hearing some proposed alternatives to WPA2, check out some of the great discussion on this Hacker News post.